Why train with us!
With a wide range of training options available, you can dip in according to your experience and ability or follow a structured route in your chosen area from beginner through to advanced professional.
We can help you find the course that will suit you and your abilities
Real-World accreditation
Our expert trainers help you achieve CP credits and industry recognised certification.
30 Day Lab Access
Our courses are built around our hands-on Hack-Labs You also get 30 days extended access included in the majority of courses.
Comprehensive roadmap
We provide a series of courses tailored to suit your needs and to suit your abilities.
Our courses, taught globally, are available as live online training
Introductory courses
Security Awareness
Introduction
Hacking 101
Introduction
Prerequisites: Hacking 101
Basic Infrastructure Hacking
Core
Basic Web Hacking
Core
Advanced Hacking
Prerequisites: Hacking 101, Art of Hacking
Advanced Infrastructure Hacking
Advanced
Advanced Web Hacking
Advanced
Hacking Cloud Infrastructure
Prerequisites: Hacking 101
Hacking Cloud Infrastructure
Specialist
Hacking Azure: From Recon to Domination
Specialist
Prerequisites: Hacking 101
Hacking and Securing Cloud Infrastructure
Specialist
Prerequisites: Hacking 101
Mastering LLM Integration Security: Offensive & Defensive Tactics
Specialist
Prerequisites: Hacking 101
AppSec for Developers
Specialist
DevSecOps
Specialist
Trusted by leading organizations
Courses to suit your need

Offensive courses
Our trainers are all professional, experienced high level Penetration Testers and whether they are teaching Basic or Advanced Infrastructure Hacking, Web Hacking or Hacking Cloud Infrastructure, they couple this experience with the latest tips and techniques and bring it all to bear on your training.

Defensive courses
An increasingly demanding and popular area in our portfolio, covering ways of securing your cloud more effectively, through to bringing security fully into your DevOps cycle in our latest series of DevSecOps courses for developers.
Courses to suit your ability
Our training courses are ideal for those preparing for CREST CCT (ICE), CREST CCT (ACE), CHECK (CTL), TIGER SST, and other similar industry certifications. In addition, those who perform Penetration Testing on infrastructure / web applications, or developers and IT professionals looking to secure their applications and cloud environments, are likely to have differing technical backgrounds. Our courses can be attended by anyone with the requisite skills and knowledge and the level of understanding you will need for each course can be seen on the relevant course details. Find the next course that suits you.
The overall structure however, provides a series of continuous paths for those wishing to start and pursue a career in penetration testing or cloud application development.


Introduction
Courses like Security Awareness, are aimed at the non IT individual, and provide an excellent understanding of cybersecurity threats and vulnerabilities and what an individual can do to help protect themselves and their company.
For the novice, the one day Hacking 101 course is a great introduction into the world of hacking and will teach the foundations of pen testing.
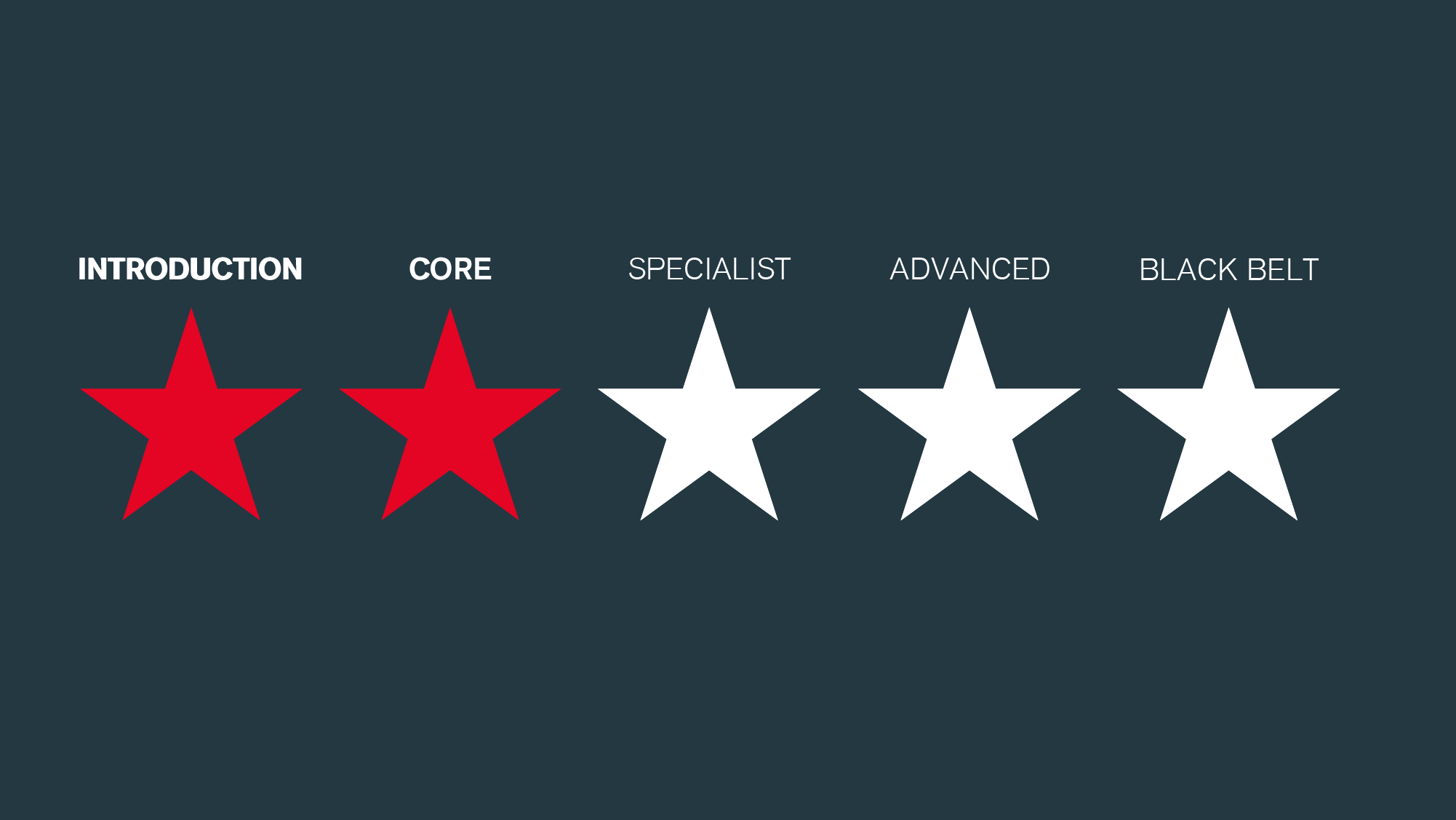
Core
Primarily offensive courses, the Core skill levels are excitingly covered in our Basic Web Hacking and Basic Infrastructure Hacking courses. Running for between 2-3 days, they are the perfect grounding for those interested in taking their first step into the world of pen testing and ethical hacking. Packed with real world examples and with full use of our Hack-Lab, they are consistently in high demand and are an excellent lead into the Advanced courses.

Specialist
Specialist more by subject than ability, these courses are specific in that they concentrate on a particular area, such as DevSecOps or Cloud Security. The defensive AppSecOps course combines our AppSec for Developers (a similar skill level to the Core courses), whereas DevSecOps (an intermediate to advanced skill level) is aimed at the more experienced security professional. Equally, Hacking and Securing Cloud Infrastructure covers both Offensive and Defensive aspects.

Advanced
These fast-paced training classes provide insight at an advanced level, covering a wealth of hacking techniques, concentrating on Advanced Web Hacking (3 day) or Advanced Infrastructure Hacking (5 day). Again delegates benefit from the advanced Hack-Lab with 30-day access after the course.
These are very often taken after a delegate has attended, and put into practice, the techniques from the Basic courses at a Core skill level.

Black Belt
Only available through our Black Hat training seminars, these are special editions of our Advanced Web Hacking and Advanced Infrastructure Hacking courses aimed directly at those attendees.
Our courses can be found at leading conferences throughout the world, and as one of the leading training companies at Black Hat, we have presented over 80 courses in the US, Europe and the far East.
Why you should train with us
We are trusted for our research into the very latest cybersecurity threats and this knowledge continually informs all our cybersecurity services. What we learn from testing in the field feeds into our training and vice versa. It's mutually beneficial.

Why come
Our courses are good. Very good. If you are preparing for CREST CCT (ICE), CREST CCT (ACE), CHECK (CTL), TIGER SST, and other similar industry certifications, our hacking courses provide the right information and knowledge. If you perform pen testing on infrastructure / web applications as a day job and wish to add to your skill set, then the exercises, demos and full access to our hack-lab will provide the hands-on experience and the practice that you need to thoroughly get to grips with what is involved.
Equally, our defensive security courses help developers and IT professionals better secure their applications and cloud environments.

Where you can find us
Our training is live and on-live. Courses are run directly by ourselves or through our training partners and in all cases, the content is created by our own team of professional trainers. The Events page has links to where you can find us and what courses we have planned. The course details provide dates and timings. If a course delivered by one of our partners suits you better, e.g. QA, Global Learning Systems, then you can still register directly from here. If you want to attend a course at one of the large conferences we are training at, such as Black Hat, Brucon, Countermeasures or various events across the globe, then these can be booked either through us or with the event themselves. We look forward to seeing you soon.

Who our trainers are
All of our trainers are also experienced professional pen testers. The content they create for each course includes current, real world experiences keeping it fresh, relevant and cutting edge and each course creator is a specialist in that particular field.
We hack. We teach.

What you need
There is both a level of understanding that is needed for each course depending on the subject and level, as well as a few technical capabilities. This may include a machine that allows you to access our hack-lab, you may need administration rights or just a browser. We will provide VPN acess to our hack-lab in our UK data centre. Details can be found on each course page.

Your day
Course lengths vary but each day is full and you will be online watching the presentation, accessing the hack-lab to perform the exercises, watching the demos and solving real problems to put into practice what has been covered in the module.
After you have registered, you will receive an email confirming your course with details of exactly what you need and ensures you are placed on the course. 2 weeks prior to the course, you receive your LIVE virtual details with joining instructions. This includes details for logging into the main course hub and passwords for the hack-lab where this is appropriate. As the course progresses, additional material is made available. This includes a student pack as well as question and answer papers for the various exercises covered. In addition, many courses provide you with a further 30-day access to the hack-lab, ensuring you really do have the time to study it properly.

What next
When you have successfully completed the course and have your certificate, then what?
Well you can use the knowledge to help take one of the cybersecurity exams, go back to your company and put the techniques into practice or perhaps use it as a spur to a greater understanding. Our training roadmap is designed to help you follow a path, whether that is in pen testing, ethical hacking, DevSecOps or in a cloud environment. In some areas, this path is straightforward and each course will provide the basic knowledge you will need to attend the next. Start with Hacking 101, go through the Core levels and on to the specialist technical training on our Advanced Hacking courses.

Book your training
Our accreditations