Stefen posted his slides on "Shocking News in PHP Exploitation". Besides talking about PHP vulnerabilities, stefen has discussed some great attack vectors for bypassing Mod-security, php-ids and WAFs.
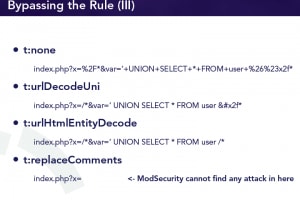
Here is a good example, from his slides, on how mod-security can be bypassed:
-----
Rules apply all transformation functions first
• t:none - reset
• t:urlDecodeUni - url decoding with unicode support
• t:htmlEntityDecode - decodes HTML entities
• t:replaceComments - removes all comments
• t:compressWhitespace - compresses whitespace
----
---